
Understanding ICMP: The Network's Messenger
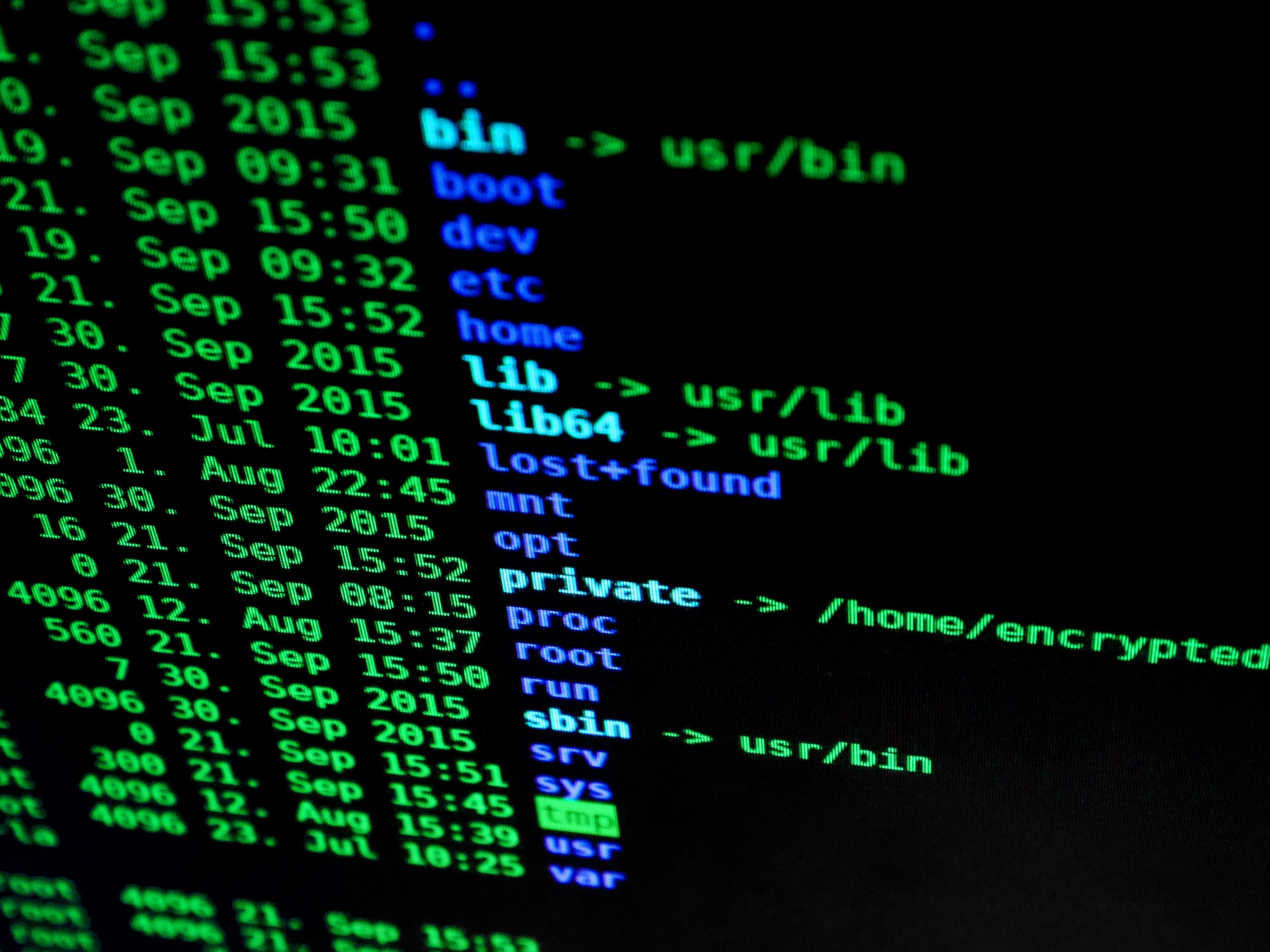
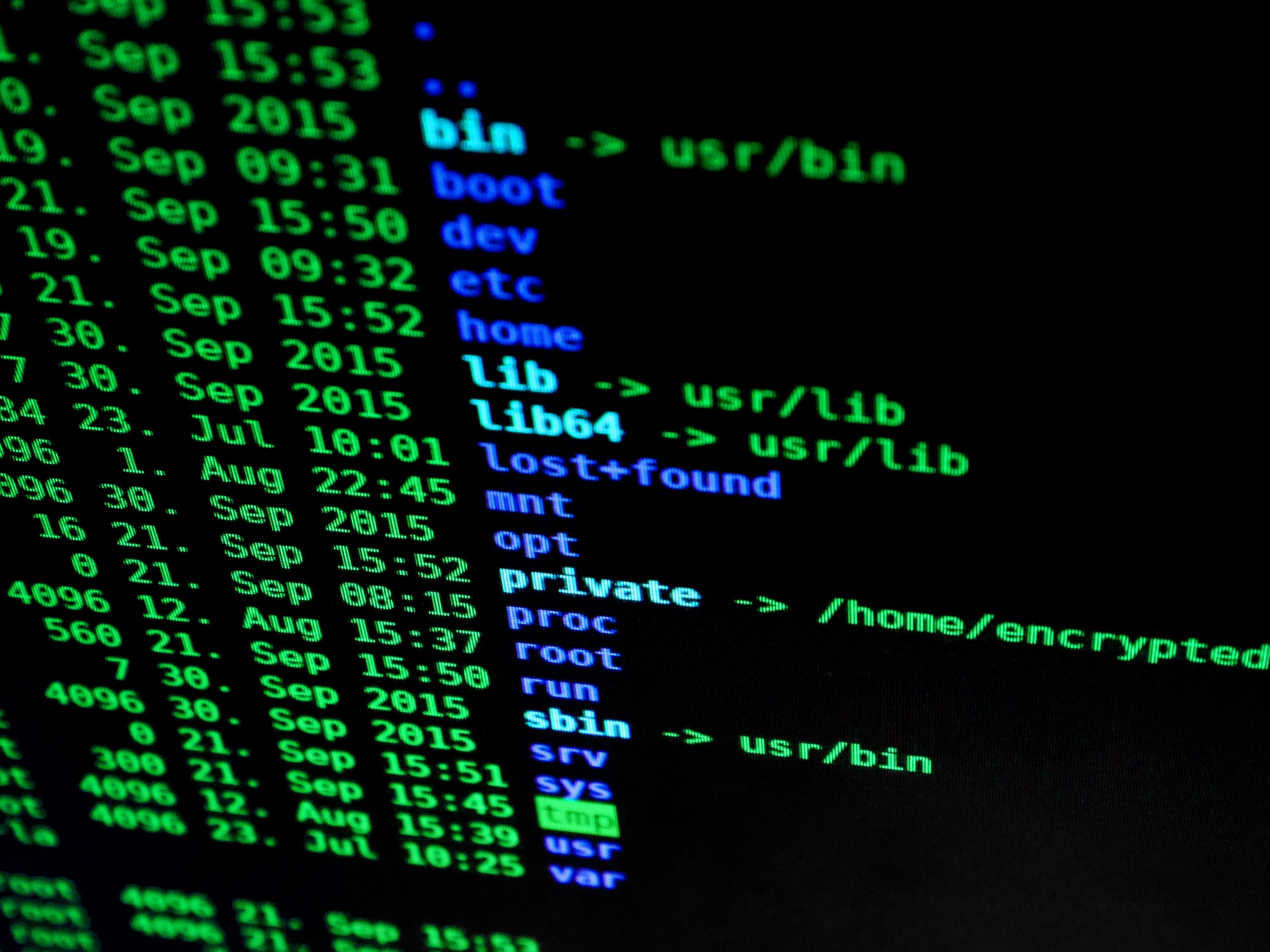
In this blog post, I'll break down ICMP in simple terms, provide Linux code examples to demonstrate its use, and include relevant images to make it all crystal clear.
Practical insights, technical tutorials, and industry analysis on modern JavaScript, AI Engineering, and mobile app development in Tunisia.

In this blog post, I'll break down ICMP in simple terms, provide Linux code examples to demonstrate its use, and include relevant images to make it all crystal clear.
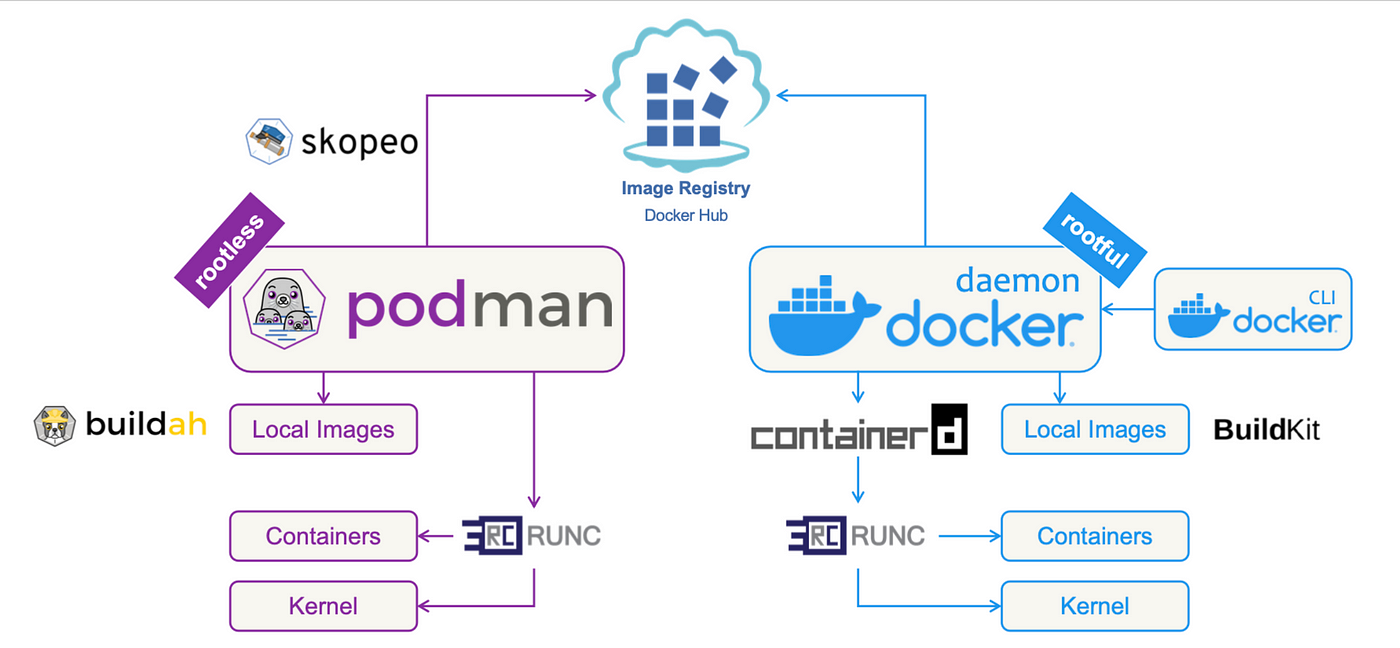
Compare Podman vs Docker in 2025: Explore key differences, security, architecture, and practical code examples to choose the best container engine for your projects.

Discover the ultimate FFmpeg guide with real-world code examples. Learn how to convert, edit, compress, and stream audio and video files using FFmpeg commands and automation.

Learn advanced Nmap techniques for network security audits, including basic scans, port scanning, OS detection, and more. Expert guide with actionable commands.
Learn how to save iptables rules after reboot using iptables-persistent, iptables-save, and netfilter-persistent. Fix common issues like service iptables-save not working or iptables-save permission denied.
Learn how to edit a rule in iptables on Ubuntu with step-by-step instructions, examples, and expert tips. Perfect for advanced users managing firewall configurations.
Learn the differences between iptables --sport and --dport, handle multiple ports, troubleshoot errors, and optimize firewall rules. Perfect for experts.
Learn how to use iptables for port redirection on Ubuntu. Explore examples like redirecting port 80 to 8080, changing destination IPs, and modifying source ports.

Learn how to implement Nginx rate limiting to protect your server from excessive traffic, DDoS attacks, and abuse. Step-by-step guide with examples.

Learn how to configure NGINX and Next.js step-by-step. This guide covers everything from basic setup to advanced optimizations for seamless deployment.

Learn how to send HTTP requests in Node.js without using external libraries like Axios. This guide covers GET, POST, and handling different content types using native http and https modules. Perfect for lightweight, dependency-free solutions.

Master Git with the top 20 essential commands for version control and collaboration. Learn Git init, add, commit, branch, merge, rebase, stash, and more with practical examples. Boost your productivity as a developer!

Learn how to implement a simple REST API in Node.js without using external libraries or a database. Step-by-step guide for building efficient APIs with the built-in http module.

Learn how to implement an HTTP server from scratch in Node.js with step-by-step guidance. Enhance your skills with examples on routing, POST handling, and graceful shutdowns.

Discover the world of lightweight hashing algorithms, including SipHash, BLAKE2, Skein, Poly1305, and FarmHash. Compare their speed, security, simplicity, and footprint to find the best fit for your applications.

Learn about TEA, a lightweight encryption algorithm, and compare it to other options like AES, DES, PRESENT, Blowfish, and Twofish. Discover its strengths, weaknesses, and when it's the best choice for your security needs.
Learn the key differences between HTTP 1.x, HTTP 2.x, HTTP 3, and gRPC. Understand their features, performance implications, and best use cases.
Discover the key differences between HTTP 1.1, HTTP 2.0, and HTTP 3.0. This comprehensive comparison table outlines the features, benefits, and advancements of each protocol.

Learn how to handle preflight requests in Deno applications using TypeScript. This guide explains CORS, preflight requests, and provides a step-by-step tutorial to set up a server that manages cross-origin interactions seamlessly.
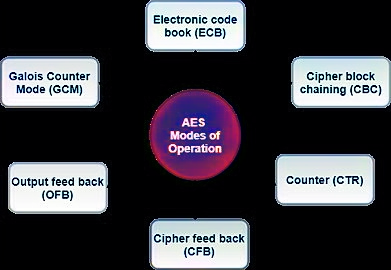
Explore the differences between AES-GCM, AES-CBC, and AES-CTR encryption modes. Learn when to use each, along with a comparison of performance, key size, resource usage, and usage scenarios.

Learn how to use the Web Crypto API to implement ECIES-like encryption and decryption in JavaScript. This article covers generating key pairs, deriving symmetric keys, and securely encrypting data using AES-GCM.

Discover the best asymmetric encryption algorithms like RSA, ECC, NTRU, and more. Compare key sizes, security, performance, and usage to choose the right encryption for your needs.

Learn how to implement AES-GCM encryption in JavaScript for secure data transmission. This comprehensive guide covers key generation, encryption, decryption, and verification.

Cryptography ECDSA to create secure digital signatures in Javascript, Deno and Node.js. This comprehensive guide covers key generation, signing, and verification, providing practical examples and best practices.

Learn how to implement secure message encryption in JavaScript using the Web Cryptography API RSA-OAEP algorithm. This guide covers key generation, encryption, decryption, and validation processes for robust data protection.

Learn about the key components of network security solutions, including, Physical Security, SIEM, IDS, IPS, firewall, VPN, encryption, and more, and how they help protect your network from cyber threats.
Discover the power of Advanced Iptables Firewall Rules for robust network security. Learn SSH brute-force protection, SYN flood mitigation, and more. Elevate your defense today!
Explore essential Iptables firewall rules and commands to secure your Linux system. Learn practical examples, installation steps, and best practices for robust network protection.

Explore the significance of Protocol TCP in modern networking. Learn about its reliability, connection-oriented nature, and the three-way handshake process. Discover why TCP is essential for seamless data transmission.

This informative guide provides a beginner-friendly introduction to the essential protocols that power the internet and enable network communication. Learn the basics of TCP/IP, HTTP, FTP, and other key protocols, and gain a deeper understanding of how the digital world works.

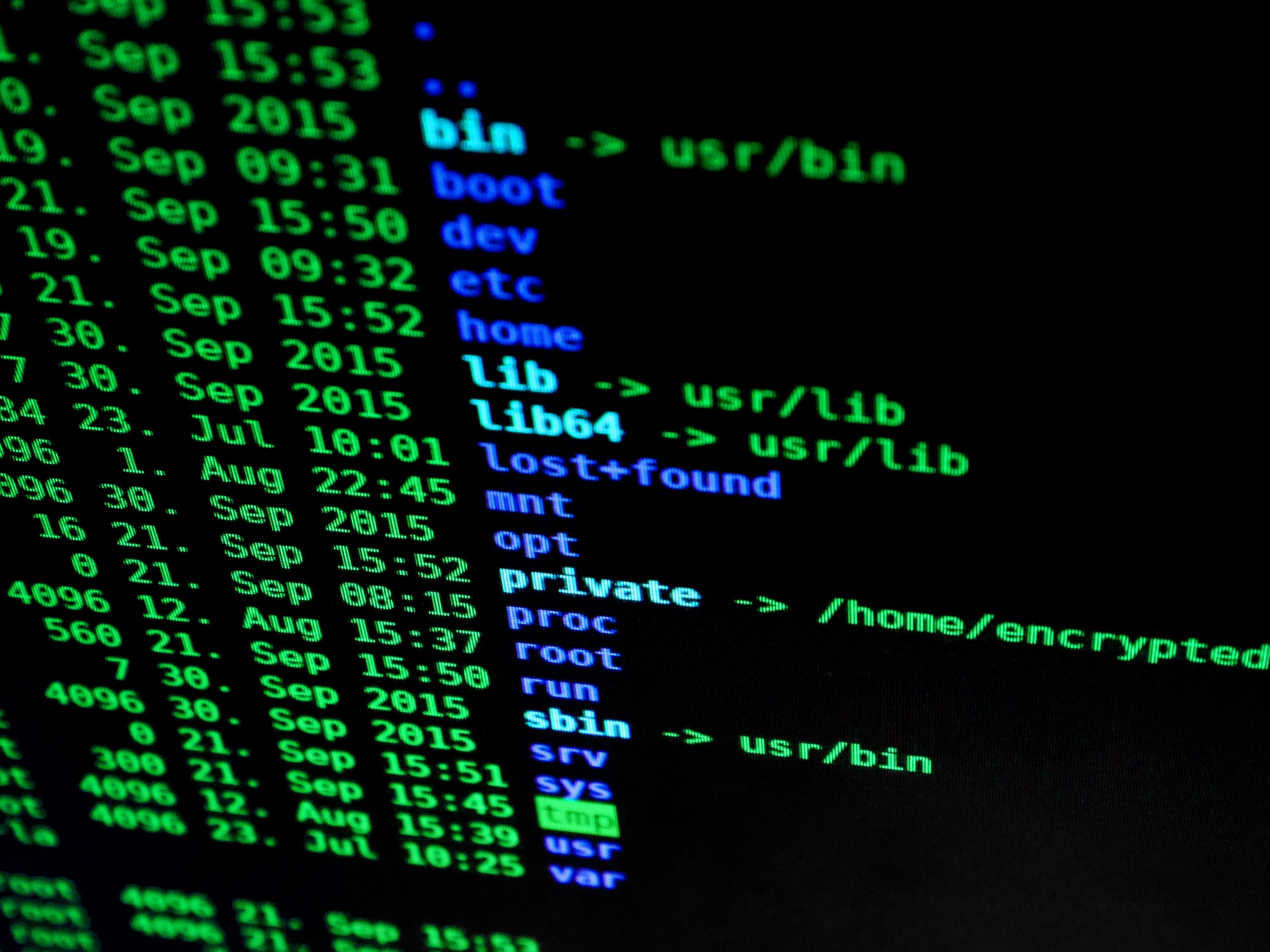
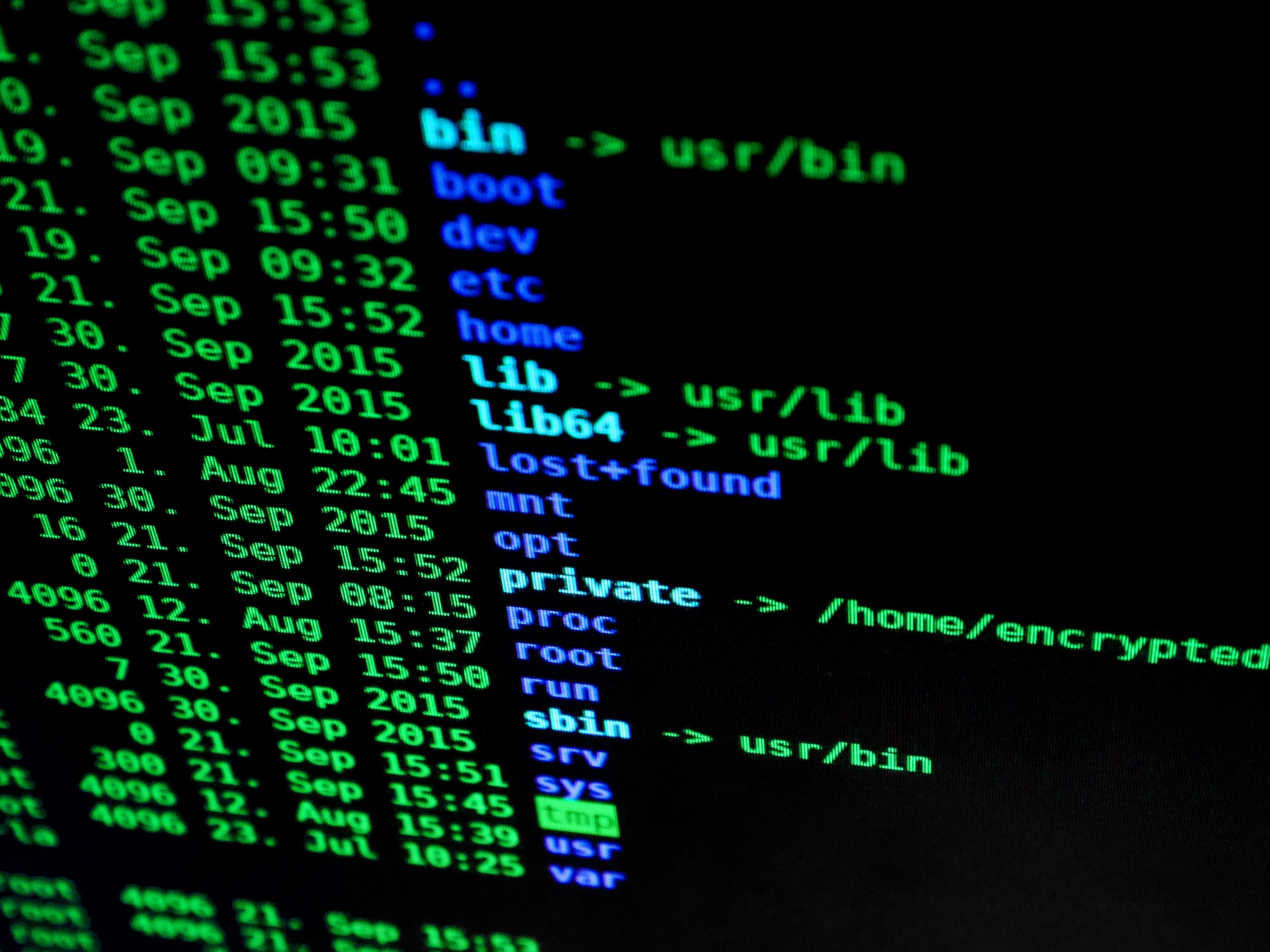
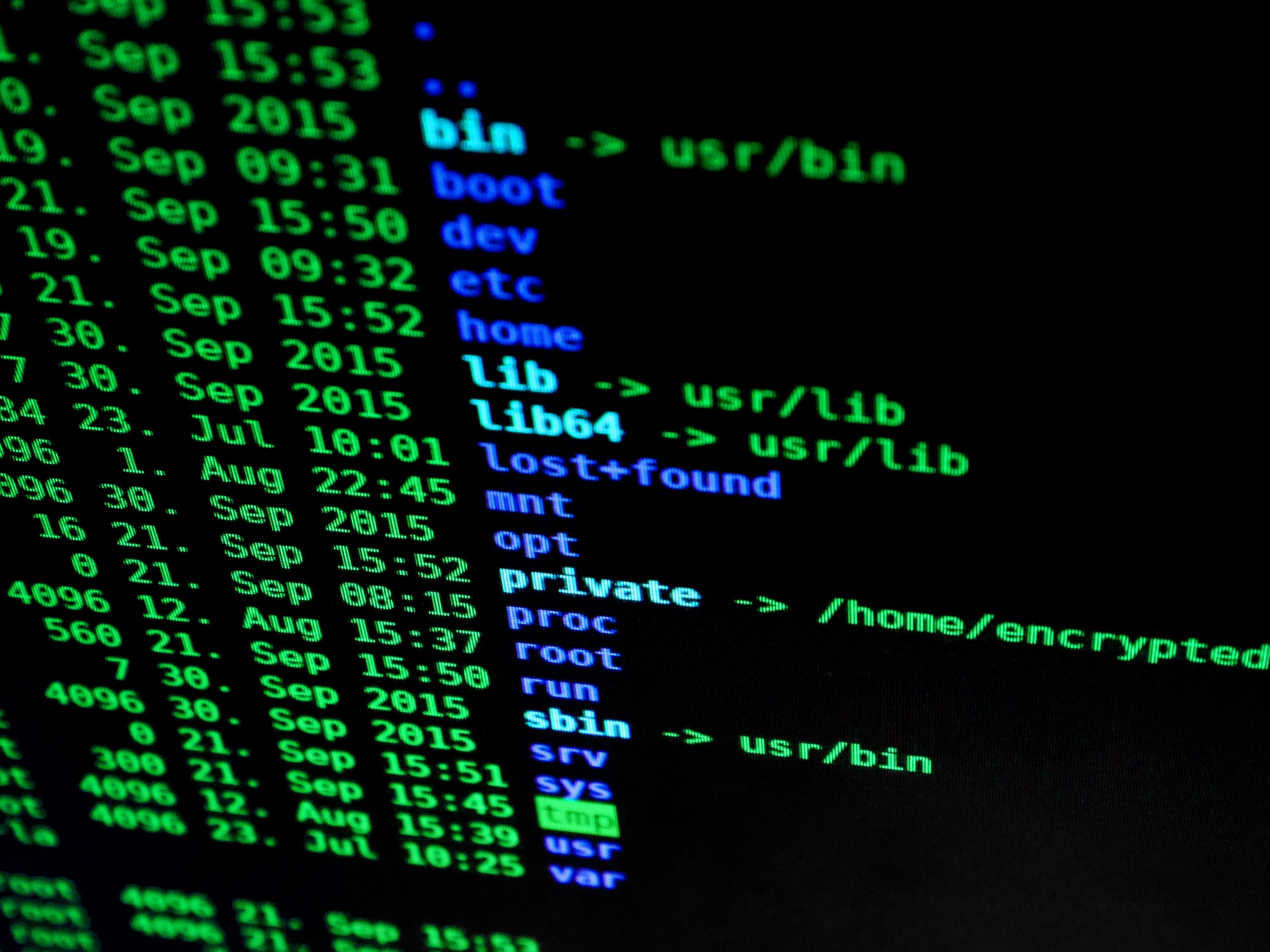
Discover the top 10 must-know tips and tricks bash shell scripting: Shebang Line, Variables and Variable Expansion, Command Substitution, Conditional Statements, Loops, Functions, Input and Output Redirection, Command-Line Arguments, Exit Status and Error Handling and Debugging.

Bash scripting with these 30 practical examples for beginner, you'll find valuable insights and ideas to enhance your productivity and streamline your workflow.
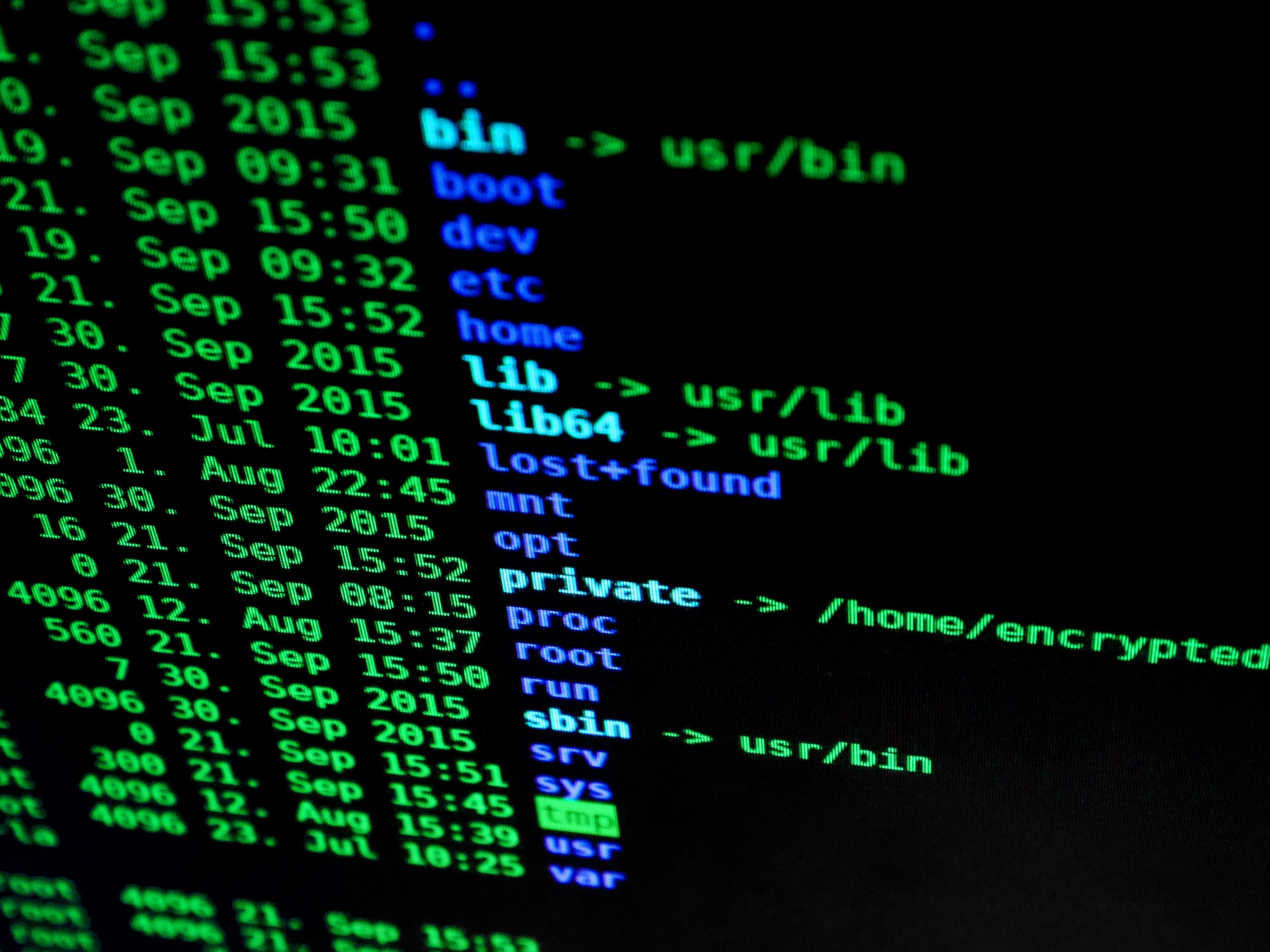
In this article, we will explore 35 useful tips and tricks for the Linux console. These tips and tricks will cover various aspects of the Linux command line and will include code examples to demonstrate their usage.